Passkeys are a secure, passwordless authentication method modeled on the FIDO2 (WebAuthn and CTAP) standards. They have several advantages over traditional identifier/password authentication:Documentation Index
Fetch the complete documentation index at: https://docs-staging.auth0-mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
- Passkeys let users authenticate with biometrics or device-bound credentials (like a fingerprint, PIN, or pattern), so login is faster and doesn’t require remembering a password.
- Passkeys synchronize credentials across devices so users don’t need to re-enroll on each new device.
- Passkeys are resistant to phishing because they use public key cryptography, so there are no shared secrets, and the user’s device generates unique keys for every account.
- Passkeys support more reliable recovery because the stored credentials can survive the loss of an originating device.
- Passkeys bind credentials to a specific domain so users can authenticate across an entire domain with a single passkey.
About passkeys on Auth0
Auth0 supports passkeys as an authentication method for database connections with three methods of implementation depending on the kind of application:- Universal Login passkeys for web-based applications
- Embedded Login native applications
- Native passkeys for Android and iOS applications
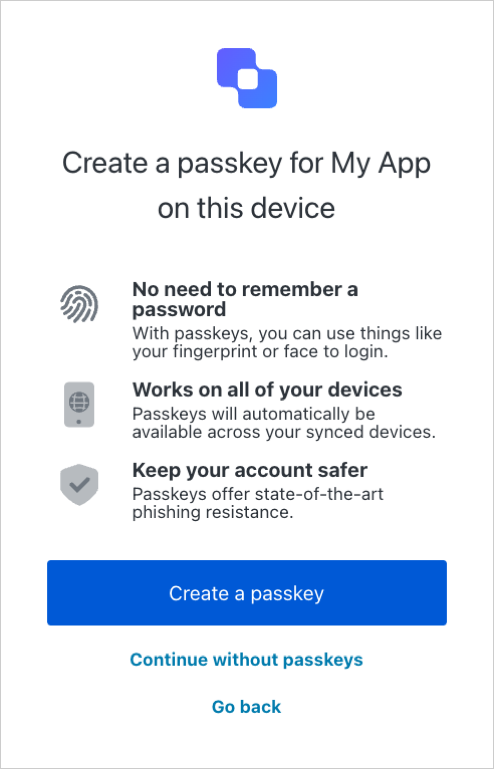
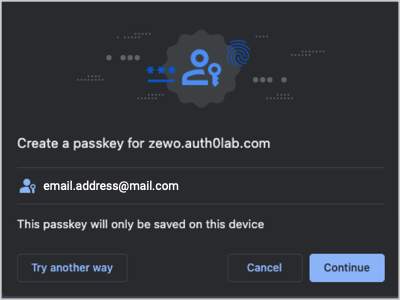
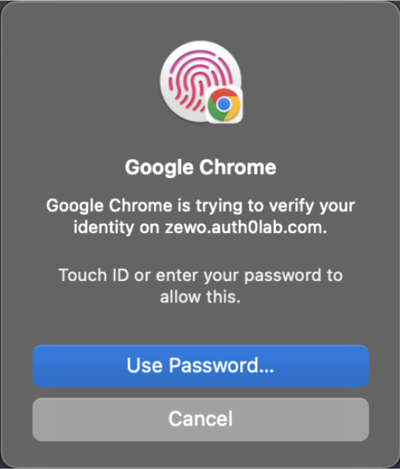
Sign-up flow preview
Sign-up flow preview
The sign-up UI prompts the user for their email address.
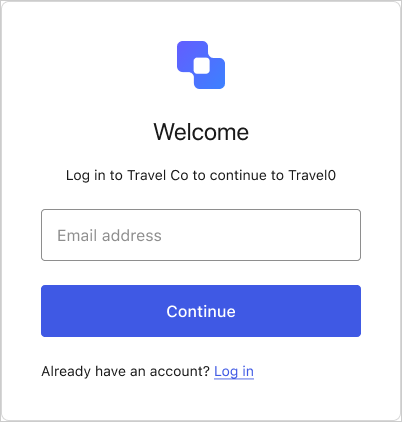
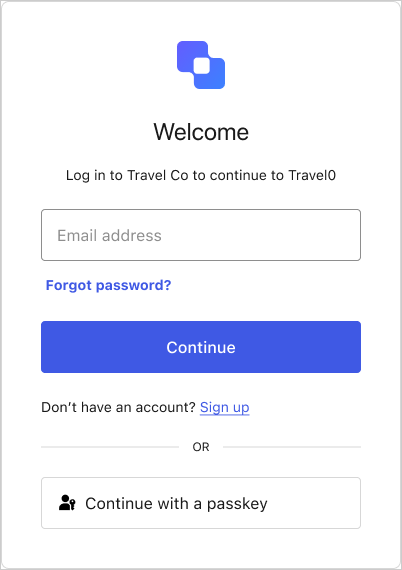
Login flow preview
Login flow preview
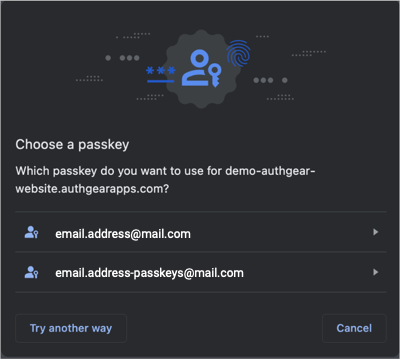
The login UI prompts the user for their email address and/or a passkey.
Your database connection’s passkey policy lets you choose whether the login UI allows autofill, displays the passkey button, or both.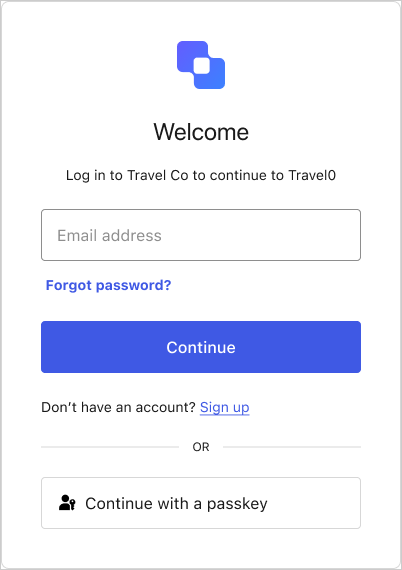 If the user enters their email, autofill suggests their stored passkeys alongside other credentials, like passwords.If the user selects the Continue with a passkey button, their credential manager prompts them to choose which passkey to use.
If the user enters their email, autofill suggests their stored passkeys alongside other credentials, like passwords.If the user selects the Continue with a passkey button, their credential manager prompts them to choose which passkey to use.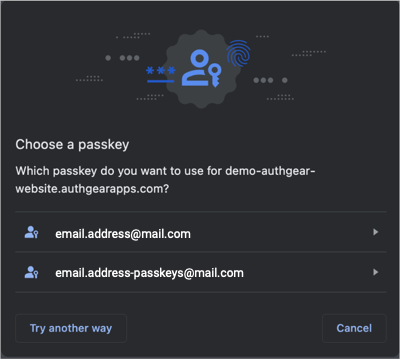
Passkeys with MFA enabled
If is enabled, the user may be prompted to complete an MFA challenge after authenticating with a passkey based on settings and risk assessment. The default behavior is to require the completion of an MFA challenge regardless if the authentication method used was a password or a passkey. Given the high level of security passkeys provide, you may skip MFA for users that have authenticated with a passkey in order to reduce friction. This can be achieved by using a post-login Action. To learn more, read Reduce friction with passkeys and Multi-Factor Authentication.Passkeys with Multiple Custom Domains (MCD)
If you have Multiple Custom Domains enabled on your tenant, Auth0 maintains a one-to-one relationship between a domain and the passkey for that domain. Users with a passkey-enabled database can sign up and log in with a passkey, tied to the specific domain it was created on. Users can enroll a passkey for only one domain (the first one they enroll with, among the multiple custom domains on the tenant). For passwordless login, the selected custom domain should be reflected in the Magic Link for the passwordless login flow.Relying party ID for Passkeys
The relying party identifier (RP ID) is a domain that WebAuthn binds to credentials like passkeys. The RP ID defines which request origins are allowed for authentication. Defining the RP ID as a suffix of the origin lets users authenticate across subdomains using one passkey. For example, if your web application is served atlogin.example.com and your native application is served at app.example.com, you can configure the RP ID to example.com so end users can authenticate both applications (and any other example.com subdomain) with a single passkey.
| Environment | Root Domain | RP ID |
|---|---|---|
| Web | https://login.example.com | example.com |
| iOS | app.example.com | example.com |
| Android | assetlinks.json | example.com |
rp.id for each custom domain.
To learn how to customize the RP ID, read Configure Passkey Policy.
Learn more
Configure Passkey Authentication
How to enable and configure passkeys as an authentication method on a database connection.
Monitor Passkey Events in Tenant Logs
Event codes and descriptions for passkey events in tenant logs.